Device & IP Analysis emits warning tags when Didit detects suspicious device, network, or location behavior. These tags are returned in decision payloads, shown in the console, and included in reports so your team can understand why a session was approved, sent to review, or declined. The device fingerprint warnings are intentionally split into exact and recovered signals:Documentation Index
Fetch the complete documentation index at: https://docs.didit.me/llms.txt
Use this file to discover all available pages before exploring further.
DUPLICATED_DEVICE_FINGERPRINTmeans the same persistent device identity was reused across sessions from differentvendor_datavalues.DEVICE_RECOVERED_HIGH_CONFIDENCEmeans v2 fingerprint recovery matched the session to a previously seen device after the persistent ID changed. This warning only appears when the match passes the high-confidence threshold and hard gates.
Automatic Decline Conditions
The following conditions always result in an automatic decline:IP_ADDRESS_IN_BLOCKLIST- The IP address used for this session is in the application’s IP blocklistDEVICE_FINGERPRINT_IN_BLOCKLIST- The device fingerprint used for this session is in the application’s device blocklist
Configurable Verification Settings
Applications can configure how the system handles various verification issues by setting actions for different risk categories:-
VPN/Proxy Detection
- Risks:
PRIVATE_NETWORK_DETECTED - Configurable action: Decline, Review, or Approve
- Risks:
-
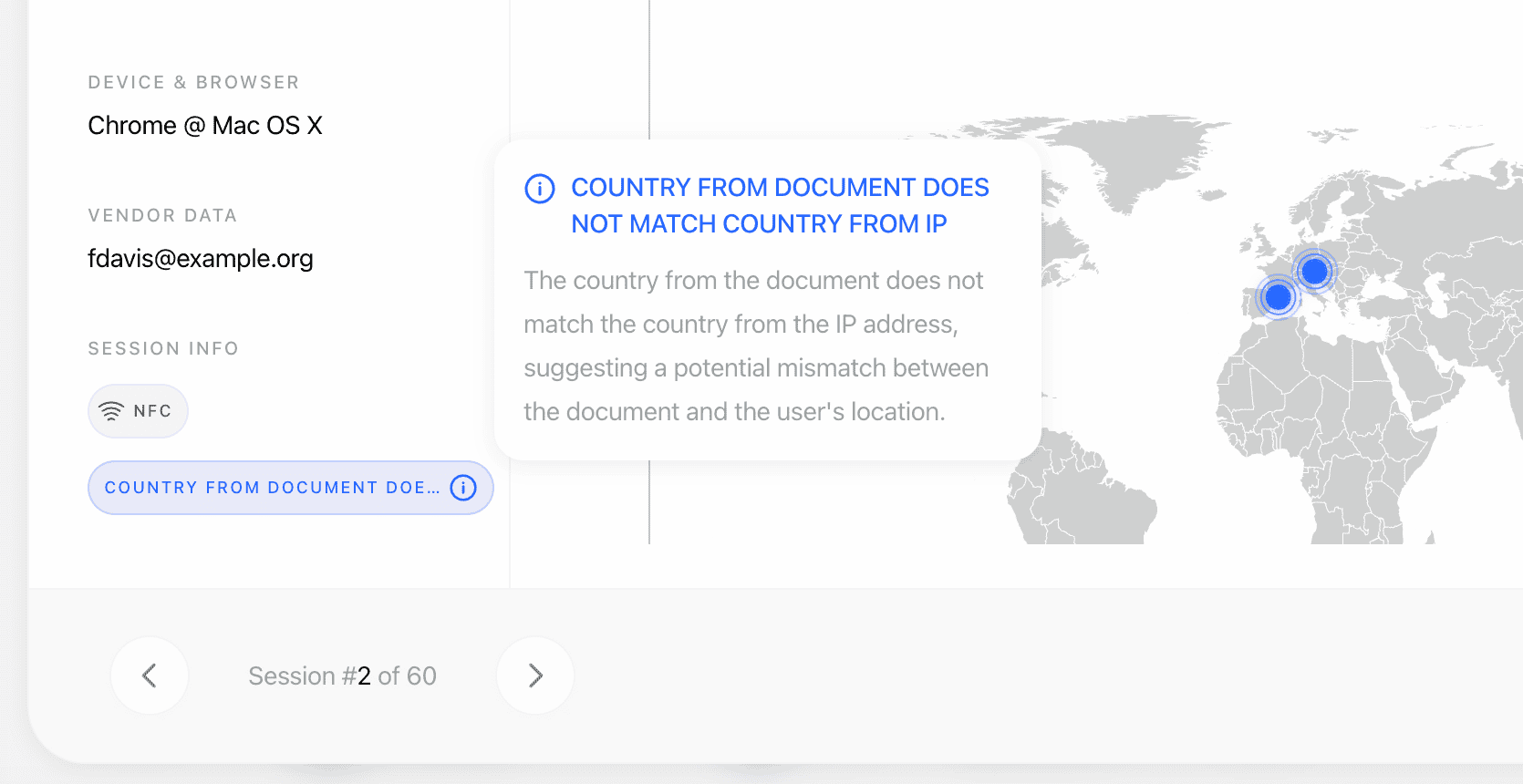
Location Discrepancy
- Risks:
COUNTRY_FROM_DOCUMENT_DOES_NOT_MATCH_COUNTRY_FROM_IP - Configurable action: Decline, Review, or Approve
- Risks:
-
Expected IP Address Mismatch
- Risks:
EXPECTED_IP_ADDRESS_MISMATCH - Configurable action: Decline, Review, or Approve
- Risks:
-
Duplicated IP Address
- Risks:
DUPLICATED_IP_ADDRESS - Configurable action: Decline, Review, or Approve (default: Approve / no action)
- Risks:
-
Duplicated Device Fingerprint
- Risks:
DUPLICATED_DEVICE_FINGERPRINT - Configurable action: Decline, Review, or Approve (default: Approve / no action)
- Risks:
-
Recovered Device Fingerprint
- Risks:
DEVICE_RECOVERED_HIGH_CONFIDENCE - Configurable action: Decline, Review, or Approve (default: Approve / no action)
- Recommended rollout: start with Review while you inspect real warning volume and match context.
- Risks:
Warning Rejection Tags
These are the Device & IP Analysis warning tags and their descriptions:| Tag | Description |
|---|---|
PRIVATE_NETWORK_DETECTED | The system detected that the user is attempting to access through a VPN, proxy, or Tor network, potentially to mask their true location. |
COUNTRY_FROM_DOCUMENT_DOES_NOT_MATCH_COUNTRY_FROM_IP | The country indicated in the user’s identity or address documents does not match the country associated with their IP address. |
EXPECTED_IP_ADDRESS_MISMATCH | One of the IP addresses used for this session does not match the expected IP address provided during session creation. |
IP_ADDRESS_IN_BLOCKLIST | The IP address used for this session was found in the application’s IP blocklist, indicating a known suspicious or forbidden origin. |
DEVICE_FINGERPRINT_IN_BLOCKLIST | The device fingerprint used for this session was found in the application’s device blocklist, indicating a known suspicious or forbidden device. |
DUPLICATED_IP_ADDRESS | The same IP address was used in another session with a different vendor_data, which may indicate multiple users sharing the same network or a potential fraud pattern. |
DUPLICATED_DEVICE_FINGERPRINT | The same device fingerprint was detected in another session with a different vendor_data, which may indicate multiple identities verified from the same device. |
DEVICE_RECOVERED_HIGH_CONFIDENCE | The v2 device fingerprint recovery model matched this session to a previously seen device with high confidence, even though the persistent device ID changed. |
Duplicate Device vs. Recovered Device
Use both warnings, but treat them differently:| Warning | Trigger | Typical meaning | Recommended first action |
|---|---|---|---|
DUPLICATED_DEVICE_FINGERPRINT | Exact persistent device identity or trusted duplicate fingerprint match. | Strong evidence that the same device appears across different users. | Review or Decline, depending on your fraud tolerance. |
DEVICE_RECOVERED_HIGH_CONFIDENCE | High-confidence v2 recovery after storage, session, or app identity changed. | Strong signal for incognito/storage reset/app reinstall attempts, but intentionally separated so you can monitor it. | Review first, then tighten after measuring your false-positive rate. |
Cross-Session Matches
When the same IP address, exact device fingerprint, or recovered device is detected across sessions belonging to different users, the system records these as matches on the Device & IP Analysis response. This helps detect when different individuals verify from the same device or network. Sessions are grouped byvendor_data: when you provide a vendor_data (your user ID), sessions with the same vendor_data are treated as the same user and excluded from matches. Without vendor_data, every session is treated as a unique user and all potential duplicates are surfaced. We strongly recommend always providing vendor_data to reduce noise.
Each match includes:
session_idandsession_numberof the matching sessionvendor_dataof the matching sessionmatch_type— eitherip_addressordevice_fingerprintmatched_value— the actual IP or fingerprint that matcheddevice_info— device brand, model, browser, OS, platform, and fingerprint of the matched sessionlocation_info— IP address, country, state, city, and VPN/data center flags of the matched session- recovered-device metadata when available, including the matched device and similarity band
matches array on both V2 and V3 decision endpoints under ip_analysis / ip_analyses.